Home-Grown Red Team: Testing Common AV Evasion With PE Packers On Windows 11
Bypassing AV solutions is essential for initial access, lateral movement and full domain compromise. Over the last couple of years, we’ve seen a myriad of various techniques, PE packers and other AV bypass solutions for pentesters to get past defenses.
But it’s 2022! Windows 11 has been released. So do the old tricks work or are they just a waste of time? I recently downloaded a Windows 11 development VM
Let’s find out!
ScareCrow
ScareCrow is a popular payload development framework. If you haven’t heard of it, ScareCrow can do a lot of things. It can enable sandbox evasion, sign a DLL or EXE with a fake cert from a legit company, and all from just a .bin file.
ScareCrow has even been implemented as a Cobalt Strike plugin. This was enough to get past Windows Defender and a lot of AV last year. Since then, Microsoft has released a lot of AMSI/Defender updates. So, does it work against Windows 11?
Let’s give it a shot with a generic Metasploit payload.
We can then use our raw shellcode with ScareCrow to create a DLL.
For the final test, I’ll host the DLL and try to download it to my Windows 11 VM.
Defender blocked our DLL! What about an EXE?
Defender blocked our EXE also! As you can see, looks like ScareCrow is out.
PEzor
Moving on to PEzor, we have a few more options. PEzor offers a lot of ways to bypass Defender and other AV engines through raw syscalls, user-land unhooking, and storing shellcode in the .text section of he PE.
We’ll use the same generic Metasploit shellcode and try a few different methods.
Here’s our first payload.
As you can see from the screenshot below, our payload was detected.
Every iteration that I used with PEzor resulted in Windows Defender catching my payload. Looks like this one is done also.
Charlotte
Charlotte is a pretty cool packer, but instead of creating EXEs it creates DLLs. The tool utilizes methods from Sektor 7’s malware development essentials course. It automates XOR encrypted payloads and provides a key to run on the target system.
Let’s use the same Metasploit payload and see if we can get past Defender.
Looks like Charlotte has been signatured by Defender also.
Sh3llter
Let’s go back in time and see if we can use the original PE packer, Sh3llter.
Sh3llter is pretty cool because it takes a 32 bit executable and loads your shellcode into it automatically.
We can download the 32 bit version of Putty and insert our shellcode.
Okay, this one was a long shot, but I was hopeful.
FourEye
FourEye is a PE packer that offers a few different methods of encrypting payloads into an EXE file. The GitHub says that it was released February of 2021, so let’s see if this can get past Windows 11 defenses.
We’ll start out with the EXE function of the packer. Let’s create our Metasploit EXE file. Notice from the screenshot below, we are using the zutto_dekiru encryption provided by Metasploit.
Now we can run this through FourEye’s XOR encryption scheme. This will give use a double encrypted EXE.
Okay, with our new Metasploit EXE encrypted, we can try it on our Windows 11 instance.
Bummer. Okay, so it’s signatured our EXE file, but what about shellcode? Let’s recreate the same payload, but in raw format.
We can run this payload through FourEye and we’ll use the second bypass option, QueueUserAPC.
Looks like the shellcode.exe file downloaded properly on Windows 11. We’re off to a great start.
Let’s see if we can run the EXE.
The meterpreter session opened! We successfully bypassed Windows Defender! But when we drop into a shell session, our payload is caught.
Looks like we have a packer that bypasses Windows 11 defenses.
Inceptor
Inceptor is a Windows based packer that offers a lot of different features. It’s python based and offers several modules for AV bypasses. The github offers very little in the realm of syntax examples so you might run into problems getting some of the modules to work.
Let’s use our Metasploit payload to see if we can get past Defender.
This command will compile an XOR encrypted EXE that has been “signed” by Microsoft.
The compiled EXE downloads without detection. Let’s see if we can get a meterpreter session.
All right! A meterpreter session opened! But on our Windows box we see this prompt. Not exactly OPSEC safe.
Also, if we drop into a shell, our payload is caught.
But from the screenshot you can see, as long as we don’t drop into a shell, we can still run commands and enumerate the system undetected. The only caveat is that command prompt.
So far, we have two PE packers that will get past Windows 11’s defenses.
NimCrypt2
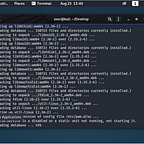
Let’s check out Nimcrypt v2. This is a rebuild of the original Nimcrypt loader. This packer allows you to unhook ntdll.dll, evade sandbox detection and use syscalls.
Using this command, I was able to get a functional executable, but it was caught by defender.
I started playing around with the flags to see if I could get the payload through, but for some reason, I couldn’t get the metasploit payload to trigger a reverse shell. So, I switched over to Covenant.
I recompiled the payload with my Covenant shellcode and was able to bypass Defender and perform process injection with this command.
On Covenant, we see that our beacon has been injected into svchost.
I was also able to bypass AMSI and spawn notepad without detection.
As you can see, Windows 11 has ramped up their defenses. Although we got caught by a lot of the PE packers out there, we were still able to get through Defender with a few.
For more red team articles, follow me on here or on Twitter @assume_breach