Home Grown Red Team: The Offensive Clipboard Revisited
This isn’t going to be a long post, but I think it’s a really cool concept that I have wanted to implement for a while. This isn’t a new idea. I have seen a few builds over the years, the most famous being WeHackPeople’s from their 18 second YouTube video.
Being 2023, the technology needed for this build has evolved and this build can be supplemented with more modern equipment. Here is he full list of gear I have used in this.
Proxmark3 with Iceman fork.
Nexus 5 with Nethunter installed
Wifi Pineapple Nano with tactical antennas
Raspberry Pi Zero W with case
Mophie battery pack
Inland USB hub
USBA to MicroUSB adapter
MicroUSB data cable (Proxmark to hub)
MicroUSB cable power only (pi to battery)
Clipboard (from Walmart)
Features
This build has a lot of features that would be used in physical red team exercises.
Badge Cloning/KeyFob Cloning
The interface for the Proxmark3 can be accessed over SSH to the Pi. While this isn’t the most efficient build from a social engineering standpoint, it’s still pretty good for just having these items laying around my lab.
Network Attacks
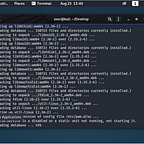
Kali tools can be loaded onto the Pi for quick access to things like Hydra, CrackMapExec, Metasploit and Ncrack and other network tools. Although there is a Kali image for the Pi Zero W, I choose Raspbian instead.
The Kali image for the Pi has always been way too slow for me. Also Raspbian offers an extremely easy setup with the Proxmark3. It’s heavily supported and most of us have either a Pi Zero or a regular Pi laying around somewhere.
With this specific clipboard, a regular Pi 3/4 would have fit without the case and still allowed for the clipboard to close.
Wifi Attacks
I was surprised that I could fit a Wifi Pinapple Nano inside the clipboard with the other gear. You might be able to use a different USB hub to fit the actual antennas in it, but having the smaller ones worked fine for me.
The pineapple allows me to easily grab a handshake (2G only) or spin up a rouge access point with just a few clicks.
Nethunter Attacks
Nethunter has a ton of attacks on it. Rucky is probably the best HID attack platform as it allows you to easily create and edit payloads through the text editor.
Paired with the Bluetooth attacks, all of the Kali tools and MiTM capability, you can easily perform penetration tests on the fly or use an ethernet adapter to leave the phone on site as a network implant.
The Other Side
The other side of the clipboard, the top, actually offers a lot of room for other gear. I could easily store lockpicks, plastic door shims, bump keys and writable badges to the other side and still be able to close the clipboard.
What Does The Networking Look Like?
All of the gear is configured to connect to my actual phone’s hotspot. I do not actually use the Nexus 5 as a cellphone. I could if I got a SIM card for it, but for now it’s just a tool.
The pi and pineapple both connect to my phone’s hotspot and I use a terminal app to quickly ssh in the pi. I use the web interface for the pineapple.
What Would Be Better?
There are a few upgrades that could be done. The proxmark3 isn’t the latest model. There is a model now that has Bluetooth and an internal battery so there would be no need for a pi.
The pi could also be upgraded to a Pi Zero W 2 or removed all together if one could get the proxmark3 firmware to work with Nethunter. I haven’t been able to get this working as there are dependency issues, but this could be because of the Nexus.
The pineapple would be much more useful if it were able to handle 5G networks (nanos can’t). Configuring a dual wifi card with the pi would be ideal but I didn’t have one laying around for the build.
The clipboard is thin enough to be able to clone badges by just putting them close to the edge of the top left corner, but a better clipboard would be recommended.
All in all, I thought this was a cool project and is awesome for testing various scenarios.
If you like this type of content, please subscribe on here or follow me on Twitter @assume-breach